OCF High Performance Computing Blog

OCF Apprentices - A pathway to success?
By Russell Billau, Lead HPC Systems Engineer
Let’s be honest: The High-Performance Computing (HPC) arena can be quite a niche field, and finding the right talented person to fit the right role can sometimes be a challenge.
AI popularity: growing trend in various industry sectors
Artificial intelligence is no longer a piece of fiction, but rather a reality that is transforming various aspects of our daily lives. AI is one of the most rapidly developing fields of technology in the world today. AI refers to the ability of machines or software to perform tasks that normally require human intelligence, such as understanding natural language, recognising faces, playing games, or making decisions. AI has many applications across various domains, such as healthcare, education, entertainment, finance, and more.
AI has become embedded throughout various industries' standard business processes, enabling them to improve efficiency, accuracy, and customer satisfaction. The global AI market size is expected to grow over 2.5 trillion U.S. dollars by 2030.
Accelerated Applications and HPC Systems: Revolutionising Industries
The rise of accelerated applications and high-performance computing (HPC) systems is transforming the way industries perform large-scale and complex computations. Traditionally, CPUs have been used to run simulations and models, but the demand for faster and more complex computations has led to the development of specialised processors such as GPUs and FPGAs that when used as accelerated can handle these workloads more efficiently. In this article, we will explore how accelerated applications and HPC systems are changing various industries and enabling companies to achieve higher levels of performance, reliability, and security.

Bridging the Skills Shortage Gap in HPC & AI with Professional Managed Services
In today's rapidly evolving tech industry, the demand for high-performance computing (HPC) and artificial intelligence (AI) expertise is soaring. However, this surge in demand has created a significant challenge for organisations: the shortage of skilled professionals to fill critical roles. Fortunately, a solution exists that can alleviate this problem and propel businesses forward. By leveraging professional managed services, companies can bridge the skills shortage gap, unlock new opportunities, and stay ahead of the competition.
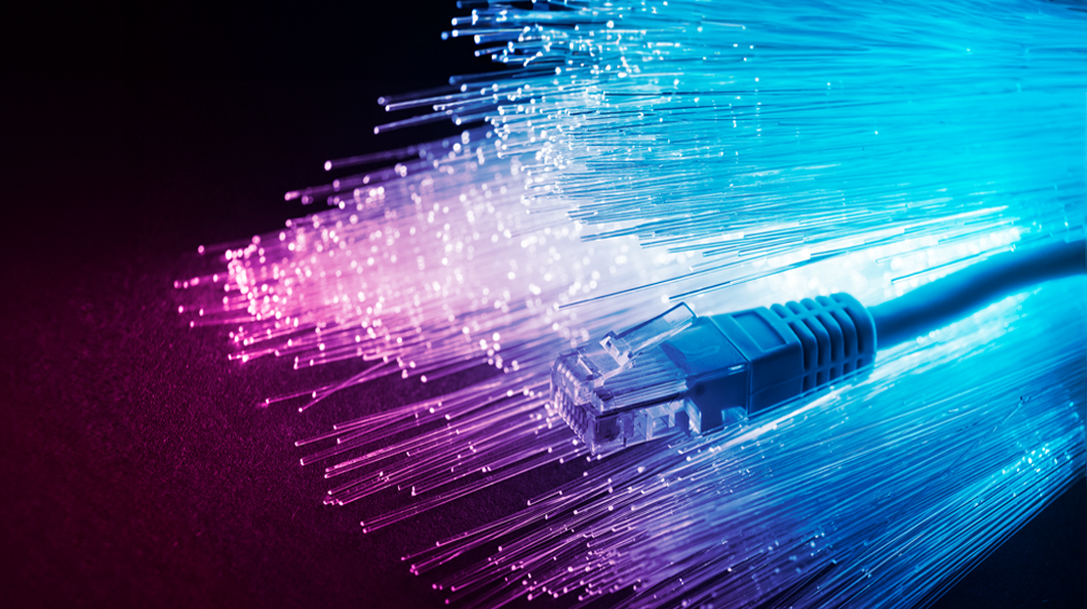
Ethernet and InfiniBand: Leading Interconnect Technologies for Different System Architectures
In the ever-expanding world of computing, system architectures must adapt to meet the increasing demands for performance, scalability, and efficiency. A crucial aspect of these architectures is the interconnect technology, which serves as the vital link between various components, enabling seamless communication and data exchange. Among the array of interconnect options available today, Ethernet and InfiniBand are the most popular in HPC environments, each offering unique strengths tailored to specific system requirements.
The Relocation of Cancer Research UK - Manchester Institute's IT Infrastructure
RJM INTERNATIONAL’S FIRST HPC CLUSTER SUPPORTS POWER PLANT EMISSIONS REDUCTIONS
RJM International, a provider of emissions reduction and combustion improvement solutions, is further able to help global power generators and other large combustion plants reduce emissions and improve efficiencies with its first high performance computing (HPC) cluster. The move also supports the growth of the company’s business in the EU and the UK, particularly in the biomass and Energy from Waste segments of the market. The new HPC environment is designed, integrated and supported by HPC, storage and data analytics integrator, OCF.
HPC For SMEs: Accelerate Tidal Turbine Simulations

